forensic/zimmer-down
- Category
-
forensic
TODO
osint/ran-somewhere
- Category
-
osint - Authors
- ,
P Percya,L LookAtThisn nalo_
The file we are given is a .eml. This file format is for emails saved in plain text. By opening it with a text editor, we can find each exchanged mails with their headers and bodys.
To open it, we could use directly a text editor, but for simplicity, we will use an email app. In our case, Thunderbird will do the job.
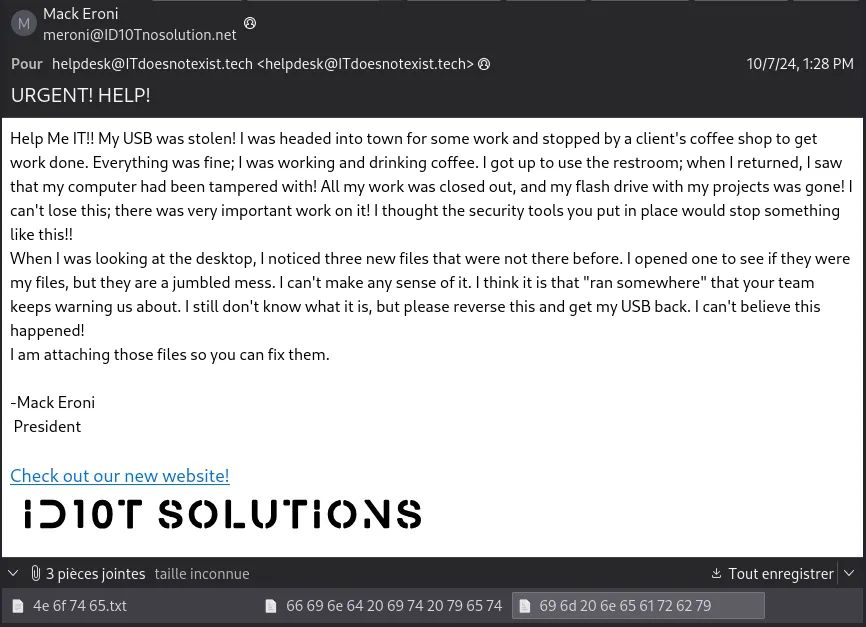
On the above screenshot, we can find some usefull information.
We learn the lore around the challenge: this guy, Mack Eroni, got his USB stick stolen at a coffee shop, and found 3 documents on the desktop. We can find the documents attached to the mail.
The first one is a text file, and the two others, without extensions, are in reality some pictures.
Translating the titles of the files from hex gives Note / find it yet / im nearby.
The content of the first file (the text one) is some bunch of hex data. Translating it again gives some text from the hacker:
$ cat "4e 6f 74 65.txt" | xxd -r -pHey There! You should be more careful next time and not leave your computer unlocked and unattended! You never know what might happen. Well in this case, you lost your flash drive. Don't worry, I will keep it safe and sound. Actually you could say it is now 'fortified'. You can come retrieve it, but you got to find it. I left a couple of files that should help.- Vigil AnteNote that I used xxd to decode the content of the file directly from the terminal, but I could have used Cyberchef as usual, it would have worked perfectly.
With this message, we now know that we need to find the place where the USB stick is waiting for us. We can note the hint “fortified” in the message, as well as “nearby” from the files title. Thus, the place should be near the caffee. But where this caffee is?? It’s where the OSINT begins.
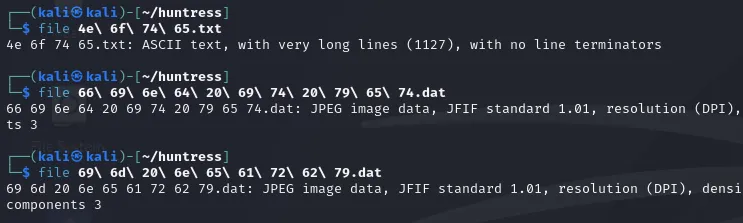
At the end of the email, we can find the link to the company’s website.
On the main page, we can find the review of the clients. The second one is saying that the salesmen drank all their coffee. It’s surely the coffee shop where Mack lost is USB key!
At the very bottom, we find the very small sentence Not Licensed to provide solutions to anyone or anywhere, especially Maryland. It certainly means they especially provide solutions in Maryland, and must be by there.
Going to Google Map, we can find a Z-Vault coffee shop in the maryland!
We now need to find the USB key nearby arround this place. But where? Well, we still haven’t used the two pictures attached to the mail. They are photography from the place we need to find. Well, that’s not a lot, but we’ll do with what we have.

Note the castle crenellations-like in the building of the first picture, and the rounded red pattern on the ground. We will use them to search on Google Map. Also a quick review of the Metadatas of the two images tells us there’s absolutely nothing.
After a bit of investingations, we found exactly those two patterns, four streets away from the coffee shop!
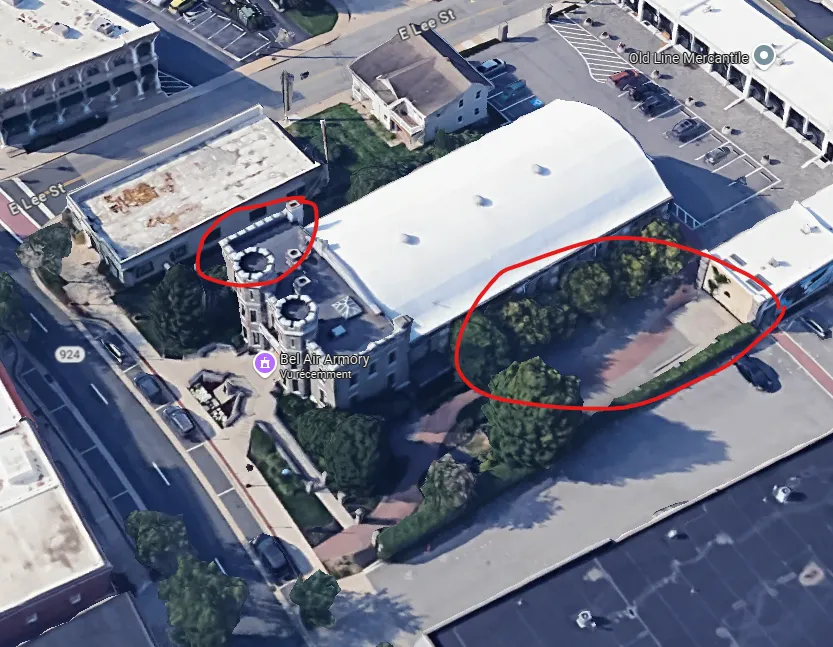
For this challenge, the flag is only the name of the place, so that’s it for this one.
misc/base-p
- Category
-
misc - Author
-
n nalo_
We are given a text file containing random character that look like chinese. In fact, they are very extended unicode characters.
As the title of the challenge says, I’m guessing it has been created using an encrypting working as base64. The later uses an alphabet of 64 characters (A-Za-z0-9+/=) to encode an input. If the content of our file is the result of a system like this, it might be using a very large alphabet.
In fact, the Unicode code point of a character from our file (obtain using python with ord('𒁊')) is 73802 (some other are 31809). In comparison, the letter A is 65.
The closest power of 2 around those numbers is 65538 (2^16). Using a Base65536 decoder, we get:
H4sIAG0OA2cA/+2QvUt6URjHj0XmC5ribzBLCwKdorJoSiu9qRfCl4jeILSICh1MapCINHEJpaLJVIqwTRC8DQ5BBQ0pKtXUpTej4C4lBckvsCHP6U9oadDhfL7P85zzPTx81416LYclYgEAOLgOGwKgxgnrJKMK8j4kIaAwF3TjiwCwBejQQDAshK82cKx/2BnO3xzhmEmoMWn/qdU+ntTUIO8gmOw438bbCwRv3Y8vE2ens9y5sejat497l51sTRO18E8j2aSAAkixqhrKFl8E6fZfotmMlw7Z3NKFmvp92s8+HMg+zTwaycvVQlnSn7FYW2LFYY0+X18JpB9LCYliSm6LO9QXvfaIbJAqvNsL3lTP6vJ596GyKIaXBnNdRJahnqYLnlQ4d+LfbQ91vpH0Y4NSYwhk8tmv/5vFZFnHWrH8qWUkTfgfUPXKcFVi+5Vlx7V90OjLjZqtqMMH9FhMZfGUALnotancBQAAThis output, even if random, exists, so it worked. In fact, that is some base64 encoded-text. Using Cyberchef, we obtain some random bytes of data, but recognized as Gunzip compressed. Decompressing it, we obtain another random bytes of data, but with the file signature of PNG file (‰PNG) at the beginning. Rendering the image, we obtain the following:
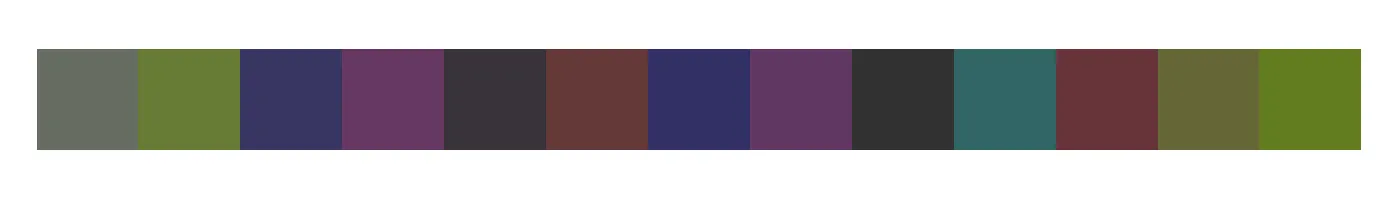
We first though about some esoteric pixel-based language like Piet, but none of the colors is actually supported.
Actually, we just need to gather all the hex color code from the 13 pixels, giving 666c61677b35383663663863383439633937333065613762323131326666663339666636617d20, and using Cyberchef, convert from hex. The result is the flag!
warmup/mystery
- Category
-
warmup - Author
-
n nalo_
Here’s the description of the challenge:
Someone sent this to me…
such enigma, such mystery:
rkenr wozec gtrfl obbur bfgma fkgyq ctkvq zeucz hlvwx yyzat zbvns kgyyd sthmi vsifc ovexl zzdqv slyir nwqoj igxuu kdqgr fdbbd njppc mujyy wwcoySettings as below:
- 3 Rotor Model
- Rotor 1: VI, Initial: A, Ring A
- Rotor 2: I, Initial: Q, Ring A
- Rotor 3: III, Initial L, Ring A
- Reflector: UKW B
- Plugboard:
BQ CR DI EJ KW MT OS PX UZ GH
The line it italic is giving us the answer of the type of encryption used for the text: The Enigma machine, used durint WW2. We could’ve guessed it with the settings (something using “rotors”).
All we have to do is to use an online decipher of enigma to retrive the content of the message:
messa gewra ppedi nligh thidd endee perou tofsi ghtlo cking itmor etigh tanyw ayyou rflag isher eflag fdfea bcacb ebfba daefb eccaa dddba fezzzWe can read some words, and by putting the spaces at the right spots, we can read the message clear:
message wrapped in light hidden deeper out of sight locking it more tight anyway your flag is here flag fdfeabcacbebfbadaefbeccaadddbafezzzAs enigma is working only using the alphabet and padding (for 4-letters blocks), we can reform the flag using the last batch of characters, keeping only the 32 firsts (ignoring the last 3 z).
